Don’t worry! We are the government! We know how to securely store data! You can trust US!
A secret terrorist watchlist with 1.9 million records, including classified “no-fly” records was exposed on the internet.
The list was left accessible on an Elasticsearch cluster that had no password on it.
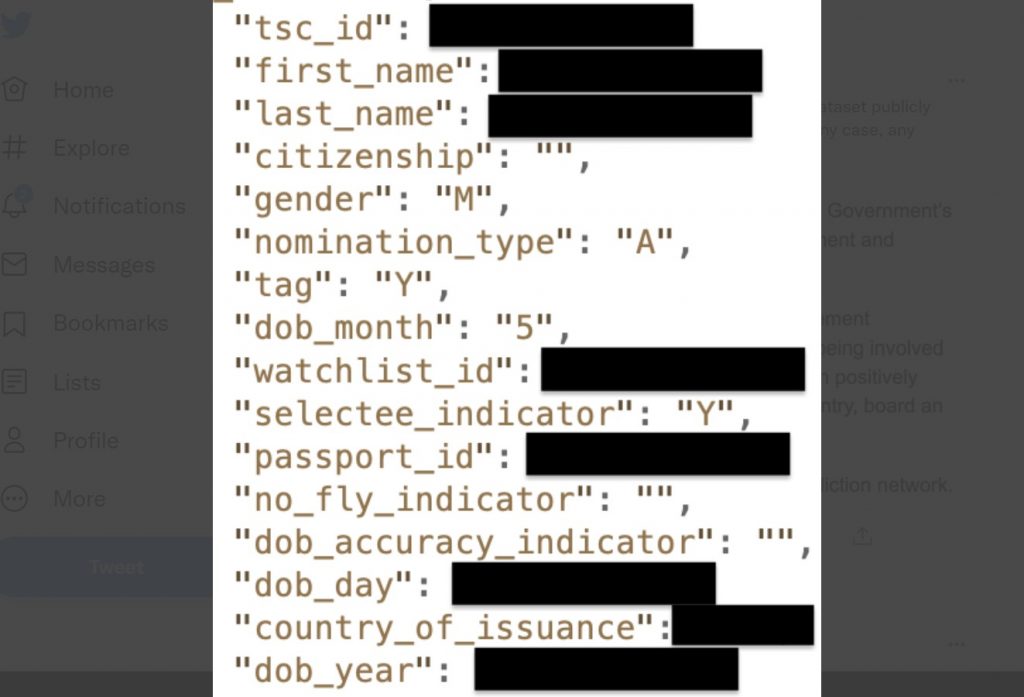
July this year, Security Discovery researcher Bob Diachenko came across a plethora of JSON records in an exposed Elasticsearch cluster that piqued his interest.
The 1.9 million-strong recordset contained sensitive information on people, including their names, country citizenship, gender, date of birth, passport details, and no-fly status.
The exposed server was indexed by search engines Censys and ZoomEye, indicating Diachenko may not have been the only person to come across the list:
Additionally, the researcher noticed some elusive fields such as “tag,” “nomination type,” and “selectee indicator,” that weren’t immediately understood by him.
“That was the only valid guess given the nature of data plus there was a specific field named ‘TSC_ID’,” said Diachenko, which hinted to him the source of the recordset could be the Terrorist Screening Center (TSC).
Apparently, this is the TSC (Terrorist Screening Centre) dataset publicly exposed (tsc_id is the only clue), with 1.9M+ records. In any case, any thoughts as of where to responsibly report? pic.twitter.com/e31pSrHnoM
— Bob Diachenko (@MayhemDayOne) July 19, 2021
FBI’s TSC is used by multiple federal agencies to manage and share consolidated information for counterterrorism purposes.
The agency maintains the classified watchlist called the Terrorist Screening Database, sometimes also referred to as the “no-fly list.”
Such databases are regarded as highly sensitive in nature, considering the vital role they play in aiding national security and law enforcement tasks.
Terrorists or reasonable suspects who pose a national security risk are “nominated” for placement on the secret watchlist at the government’s discretion.
The list is referenced by airlines and multiple agencies such as the Department of State, Department of Defense, Transportation Security Authority (TSA), and Customs and Border Protection (CBP) to check if a passenger is allowed to fly, inadmissible to the U.S. or assess their risk for various other activities.
Server taken offline 3 weeks after DHS notified
The researcher discovered the exposed database on July 19th, interestingly, on a server with a Bahrain IP address, not a US one.
However, the same day, he rushed to report the data leak to the U.S. Department of Homeland Security (DHS).
“I discovered the exposed data on the same day and reported it to the DHS.”
“The exposed server was taken down about three weeks later, on August 9, 2021.”
“It’s not clear why it took so long, and I don’t know for sure whether any unauthorized parties accessed it,” writes Diachenko in his report.
The researcher considers this data leak to be serious, considering watchlists can list people who are suspected of an illicit activity but not necessarily charged with any crime.
“In the wrong hands, this list could be used to oppress, harass, or persecute people on the list and their families.”
“It could cause any number of personal and professional problems for innocent people whose names are included in the list,” says the researcher.
Cases, where people landed on the no-fly list for refusing to become an informant, aren’t unheard of.
Diachenko believes this leak could therefore have negative repercussions for such people and suspects.
“The TSC watchlist is highly controversial. The ACLU, for example, has for many years fought against the use of a secret government no-fly list without due process,” continued the researcher.
Note, it is not confirmed if the server leaking the list belonged to a U.S. government agency or a third-party entity.
Now think about that: The government doesn’t know how to securely store (your) data! They are constantly spying on us with cameras and trojans everywhere. And now, they will start digitalizing our health data… But don’t worry! All these data are completely safe and will never surfaced anywhere! Stop this! [LinkedIn, Bleeping Computer]
Now subscribe to this blog to get more amazing news curated just for you right in your inbox on a daily basis (here an example of our new newsletter).
You can also follow us on Facebook and/ or Twitter. And, by the way you can also make a donation through Paypal. Thank you!
You should really subscribe to QFiles. You will get very interesting information about strange events around the world.













News from (clown) radio show saying some (false flag) spook in a truck by library of Con-gress making threats.
Here we go. Pretty sure truck will have Trump bumper stickers care of clownheads.
https://www.infowars.com/posts/california-resists-covid-madness-watch-fired-up-citizens-stand-up-to-mask-mandates/
San Diego Ca:
The first video is exactly what every person should be saying out loud to tyrants, in every city, and county in the U.S.A.
That lady is so awesome!
https://www.thegatewaypundit.com/2021/08/vax-entration-camps-australian-government-builds-mandatory-quarantine-facilities-officials-say-jab-golden-ticket-freedom/
Look at Australian gestapo beat women and pepper spray children for lack of masks. Then chuck them into the paddywagon. Kung-flu concentration camps.
Asinine! Where are the men? Go kick their ass right now!
Welcome to New World Order of elites that make prison planet .
The Taliban knocked on her door 3 times. The fourth time, they killed her
By Anna Coren, Sandi Sidhu, Abdul Basir Bina and Hilary Whiteman, CNN
Updated 2337 GMT (0737 HKT) August 17, 2021
(CNN)Najia was at home with her three young sons and daughter in a small village in northern Afghanistan when Taliban fighters knocked on their door.
Najia’s daughter Manizha, 25, knew they were coming — her mother had told her they’d done the same thing the previous three days, demanding that she cook food for up to 15 fighters.
“My mother told them, ‘I am poor, how can I cook for you?'” said Manizha. “(The Taliban) started beating her. My mother collapsed, and they hit her with their guns — AK47s.”
Manizha said she yelled at the fighters to stop. They paused for a moment before throwing a grenade into the next room and fleeing as the flames spread, she said. The mother of four died from the beating.
The deadly July 12 attack on Najia’s home in Faryab province was a chilling preview of the threat now facing women across Afghanistan after the Taliban’s takeover of the capital Kabul. CNN is using aliases for Najia and Manizha to protect their identity for safety reasons.
In 10 days, Taliban militants captured dozens of provincial capitals left vulnerable by the withdrawal of US and allied troops.
The speed of the militants’ advance caught locals off guard.
Some women said they had no time to buy a burqa to comply with Taliban rules that women should be covered up and accompanied by a male relative when they leave the house.
To Afghanistan’s women, the flowing cloth represents the sudden and devastating loss of rights gained over 20 years — the right to work, study, move and even live in peace — that they fear will never be regained.
Workers at a beauty salon strip large photos of women off the wall in Kabul on August 15, 2021.
Unconfirmed report says Taliban killed 4 Women Jet Fighter pilots. Islam lies do not believe they says we come in peace. There will be soon blood bath which started in Afghanistan will be mother of blood baths .
Bomb bomb Taliban 100k forces and also Iran for regime change.
It’s really too bad DHS was notified of this leak, because that gave them the opportunity to continue to cover up *THEIR* crime of targeting innocent people like myself and three family members. Sadly, I know more than I ever wanted to know about DHS et al illegally targeting / blacklisting innocent people!
It’s not even a legal or constitutional agency just like the other 100+ they have created up there.
They exist to reinforce those up there and has nothing to do with your safety or care. Maybe theirs but that’s about it.
The DHS will be used for a much greater OPPRESSION, than anything else.
“Reported to the DHS”? You mean the Department of NAZI Security, NOT the American People. Sorry to need to inform your IGNORANCE, but the 2nd Amendment IS Homeland Security, and it rests within the hands OF THE PEOPLE, not an Illegitimate Criminal Usurpation of our BLOOD BOUGHT CONSTITUTION, contrived through False Flag FRAUD by BRITISH Windsor/Rothschild Banker minions – the ENEMIES of mankind. Anyone that would even associate or acknowledge, to give credence to, with this UNCONSTITUTIONAL AFFRONT called the DHS, is a MORON to begin with. A DUPE with no clue as to the true Security and well-being of America, or the LAW and Constitution that is OWNED BY THE PEOPLE. get your head out of your @$$ and figure it out. These same DELUSIONS brought us Joe Biden and the demise we now face. Time to wise the hell up.
??????????????
Hahaha,
Rather drive anyways. Most people in the airline biz are whining inbeciles that think their shjt doesn’t stink. Many have the delusion they are super important people too. Laughable.
And that ‘list’ has innocent people on it cuz their name is ‘similar’ to real terrorists…never trust the ‘Intel’ community ever.
I know. Right now I wish I were Polish or Hungarian by blood.
God is less likely to punish their countries.
Maybe I can identify as a Hungarian?
lolollolllollllolllll